PCI compliance call center guide: the 4.0.1 update, industries, hidden costs & how-tos
%20(1).webp)
TL;DR: PCI DSS 4.0.1 is fully enforced, pause-and-resume is no longer acceptable, and any system that could inadvertently receive cardholder data is now in scope by default. For companies outsourcing customer support, that means your vendor's certification gap becomes your liability. This guide covers what changed, what it costs to ignore it, which industries carry the highest risk, and what genuinely compliant outsourced support looks like in practice.
Call center PCI compliance isn't optional – and with PCI DSS 4.0.1 now fully enforced, it's also no longer as simple as hitting "pause" before a customer reads their card number.
According to IBM's 2024 Cost of a Data Breach Report, the global average cost of a data breach reached $4.4 million – a 10% increase year over year.
For companies outsourcing customer support, that exposure doesn't disappear just because the call is handled by a third party. It follows the data.
Why PCI DSS 4.0.1 is a game-changer for call center outsourcing
PCI DSS 4.0.1 – the latest revision of the Payment Card Industry Data Security Standard – became fully mandatory on March 31, 2025. The update didn't overhaul everything, but the changes it made hit contact centers squarely in the operations.
The headline shift: any system that could inadvertently receive or transmit cardholder data is now in scope by default. Previously, teams could argue their way out of scope with narrow definitions. That grey area is gone.
What this means in practice:
- Pause-and-resume is no longer acceptable. The approach of pausing call recordings while a customer reads out card details doesn't prevent the data from being heard by an agent, captured in screen logs, or stored in ancillary systems. PCI DSS 4.0.1 explicitly demands a proactive, not reactive, approach to data protection.
- Scope creep is the enemy. Businesses must now audit every system – from call center phone systems to chat logs – to confirm whether cardholder data can reach them. If it can, that system is in scope.
- Multi-factor authentication (MFA) is mandatory for all access to the cardholder data environment, no exceptions for remote workers or third-party agents.
- Tokenization and DTMF masking – where customers input card numbers via their keypad, bypassing agent ears and call recording entirely – are now the accepted standard for inbound calls where payments are taken.
The bottom line for outsourcing: if your BPO partner isn't already operating in a zero-scope or descoped cardholder data environment, your brand carries the risk.
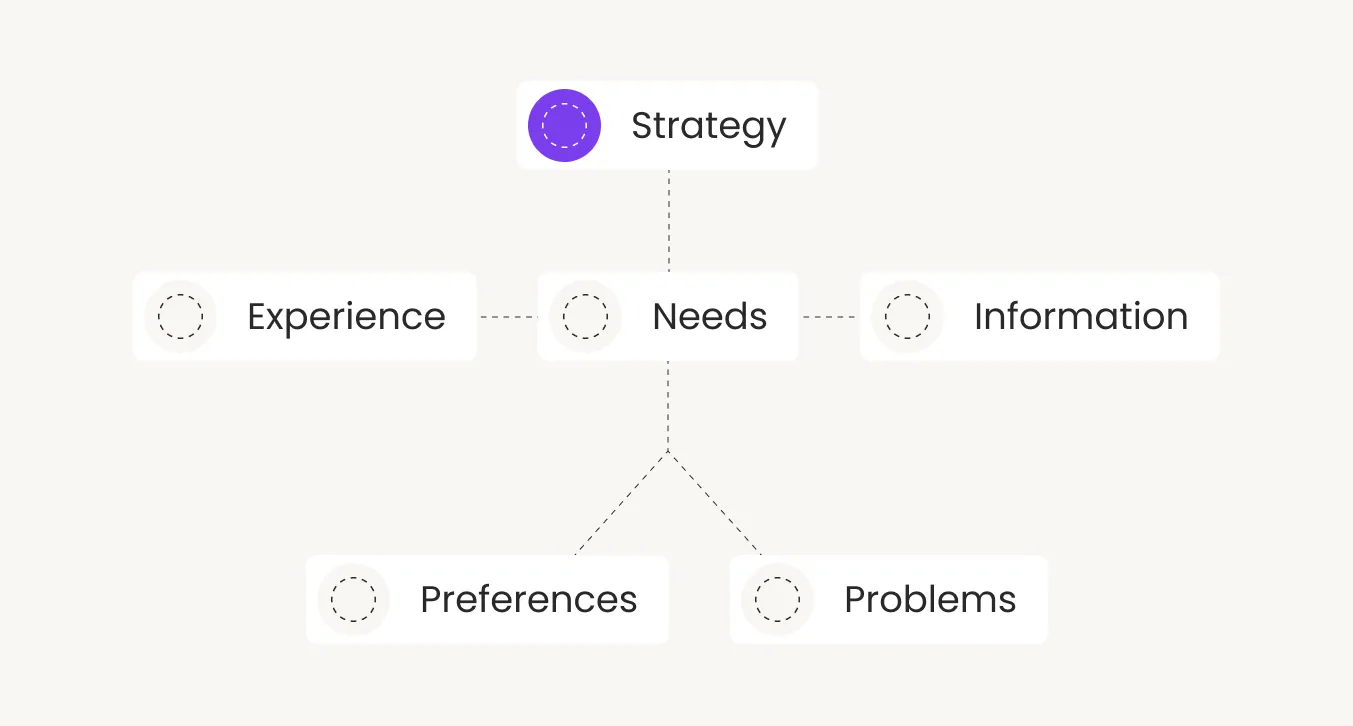
PCI call center compliance requirements by industry
Compliance looks different depending on where your business operates, be it eCommerce, SaaS, fintech, or other sectors. The core requirements of PCI DSS apply universally, but the practical implications – and the business risk of getting it wrong – vary significantly by industry.
eCommerce and retail
Where it applies:
Both sectors handle high-volume, card-not-present transactions across multiple support interaction types. The risk profile is consistent across both, but spikes hard during peak periods like Black Friday, when controls that hold at normal volume can quietly buckle under pressure. Common in-scope interactions include:
- Order payment queries and failed transaction troubleshooting;
- Refund processing and card verification requests;
- Click-and-collect payment disputes;
- Loyalty point redemptions tied to payment accounts.
Requirements:
- Agents must never have access to full PANs; all payment reference data in CRM and order management systems must be masked or tokenized at the data layer, not just the UI level – a distinction that matters during platform updates and integrations.
- eCommerce integrations with platforms like Shopify and Magento must route payment data through tokenized environments before any agent interaction occurs.
- Refund workflows must trigger through the original payment gateway only; card re-entry by agents is not permitted under any circumstances.
- Call recordings must exclude any segment where card details are spoken; DTMF suppression or IVR-based capture is the accepted standard for phone-based payments.
- Screen recording tools and QA software used for agent monitoring must be configured to exclude any field where payment references appear.
- Seasonal and temporary agents must complete full PCI compliance training before handling payment-related contacts – the same standard as permanent staff, no exceptions.
- Network segmentation must remain intact during high-volume surges; infrastructure changes made to handle peak load must not inadvertently expand the PCI scope boundary.
Fintech and financial services
Where it applies:
Fintech support sits at the intersection of PCI DSS and regional financial regulation, meaning a single support call can trigger multiple compliance obligations simultaneously. The exposure is compounded – and harder to isolate than in most sectors. Typical in-scope interactions include:
- Account verification calls involving payment credentials;
- Billing dispute resolution and payment escalations;
- Fraud investigation queries;
- Plan upgrade or downgrade calls where billing changes are made.
Requirements:
- MFA is mandatory for all agent access to cardholder data environments, including for remote team members.
- Call center quality assurance frameworks must include compliance monitoring at the interaction level – not just CSAT or AHT tracking.
- Agents handling fraud-related queries must operate within clearly defined data access boundaries, with no visibility beyond their specific role scope.
- Any third-party tools used in the support workflow (AI assistants, screen-sharing tools, CRM plugins) must be assessed for PCI scope impact before deployment.
- Incident response SLAs must include card data breach notification timelines aligned with both PCI requirements and applicable financial regulations.
SaaS
Where it applies:
SaaS support teams encounter cardholder data more often than most companies realize. The risk isn't always obvious – it creeps in through the edges of ordinary billing conversations, especially as products scale and support volume increases. Common in-scope interactions include:
- Failed payment recovery calls;
- Subscription plan upgrades and billing adjustments;
- Enterprise contract renewals involving payment method changes;
- Billing dispute resolution.
Requirements:
- Support agent desktops must be descoped from the cardholder data environment; billing queries should be handled through tokenized payment references, not raw card data.
- Subscription management tools integrated into the support stack must be assessed for any cardholder data passthrough.
- Agents handling billing escalations should follow scripted payment-related workflows with no capability to retrieve or store card credentials.
- Regular vulnerability assessments should cover the full tech stack used by the support team, including any quality assurance software that logs interaction data.
Healthcare and medtech
Where it applies:
Patient billing support operates under two compliance frameworks simultaneously. HIPAA governs health information; PCI DSS governs payment data. In practice, a single call – a patient querying a co-pay charge, for example – can involve both, and the data environments must be kept cleanly separate. Typical in-scope interactions include:
- Patient billing queries and co-pay clarifications;
- Insurance gap payment processing;
- Refund requests for canceled appointments or procedures;
- Subscription billing for medtech platforms and digital health tools.
Requirements:
- Cardholder data environments and protected health information (PHI) environments must be architecturally separated, with no overlap in storage, access controls, or transmission paths.
- Agents must be trained specifically on dual-framework obligations, understanding which data type they're handling at any point in an interaction.
- Payment processing for patient billing must use a PCI-compliant payment gateway; agents should never verbally confirm or repeat card numbers back to callers.
- All call recordings involving billing queries must exclude sensitive authentication data, with DTMF masking or IVR capture in place for phone-based payments.
- Third-party billing platforms must hold current PCI DSS certification and be contractually obligated to maintain it throughout the engagement.
Travel and hospitality
Where it applies:
Travel support handles some of the highest-value, highest-frequency payment interactions in customer service – often under time pressure, which makes compliance shortcuts tempting and consequential. The customer experience in call center environments for travel brands demands fast, seamless resolution without data risk. Common in-scope interactions include:
- Last-minute booking changes involving new payment methods;
- Cancellation refunds processed over the phone;
- Loyalty point redemptions tied to payment accounts;
- Urgent rebooking during disruption events where payment credentials are reconfirmed.
Requirements:
- Agents processing refunds must work through the original payment method reference only; no direct card data entry or retrieval should be required or permitted.
- For phone-based bookings or payment changes, DTMF masking must be in place so card input bypasses agent hearing and recording systems entirely.
- High-season volume spikes – peak booking windows, travel disruption events – must not create exceptions to standard compliance controls; surge staffing must be trained and certified to the same standard as core agents.
- Loyalty account data linked to payment credentials must be stored and accessed separately, with role-based controls limiting agent visibility to the specific redemption in question.
- All inbound calls where payment changes are made must be logged with masked data references for audit trail purposes.
PCI DSS compliance risk by industry: a quick summary
The hidden costs of non-compliance
The fines get the headlines, but the real cost of failing call center PCI compliance sits in several layers.
Card networks can impose penalties of $5,000 to $100,000 per month on acquiring banks for non-compliant merchants – costs that quickly flow downstream to the business. A confirmed breach typically triggers forensic audit costs, mandatory remediation programs, and in some cases, the temporary suspension of card processing rights. For a company that depends on card-based revenue, that's existential.
Then there's the breach itself. The average financial services breach costs over $6 million, according to IBM's 2024 data, with healthcare breaches running even higher. Reputational recovery is slower and harder to quantify – customer trust, once broken over a payment data incident, rarely fully returns.
Three cost categories operators often miss:
- Increased transaction fees. Non-compliant merchants can be reclassified by card networks, triggering higher interchange rates on every transaction.
- Cyber insurance exclusions. Many insurers now specifically exclude breaches resulting from PCI non-compliance, meaning the policy you're counting on may not pay out.
- Operational disruption. Post-breach remediation pulls internal teams away from contact center workforce optimization and growth work for months.
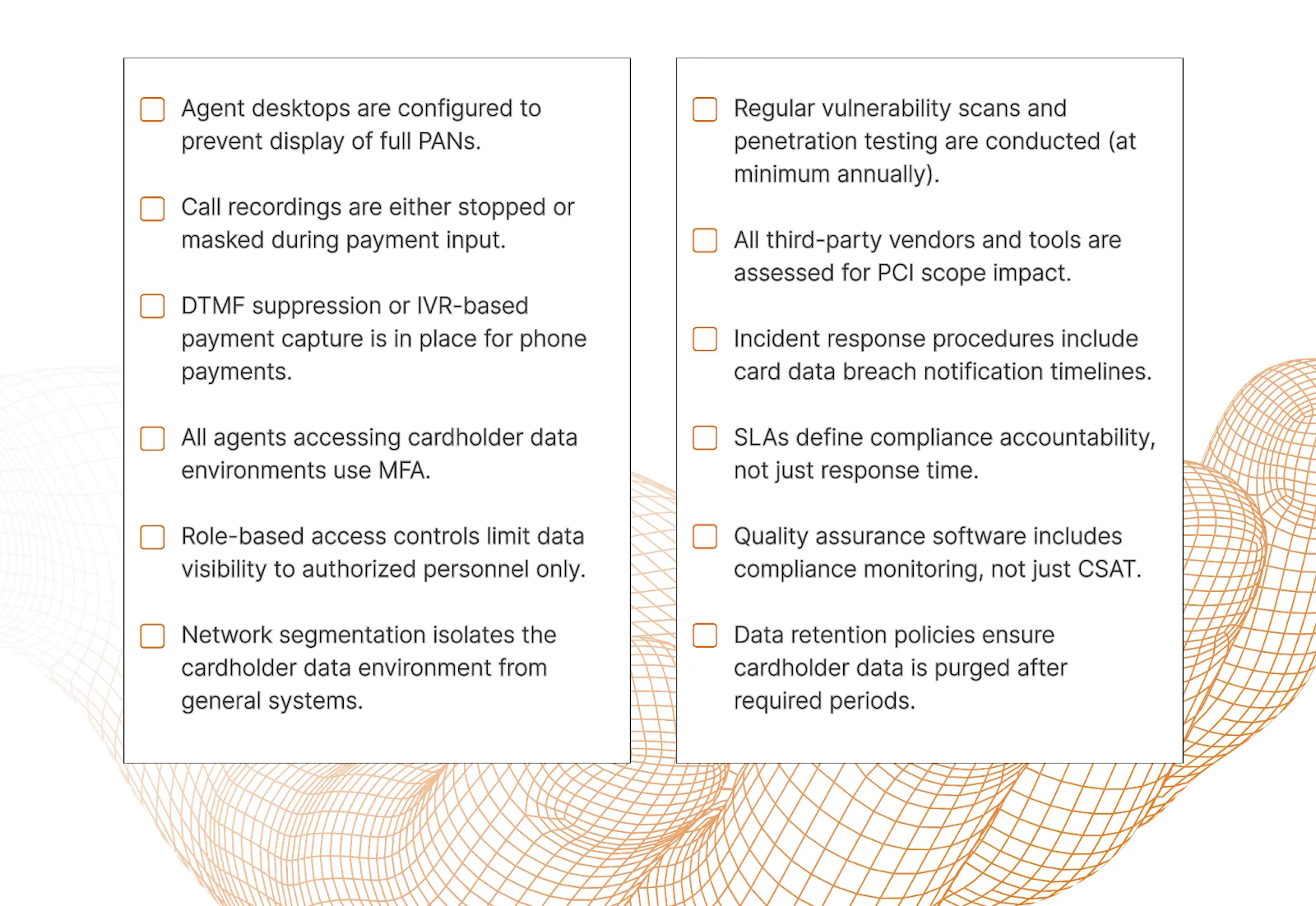
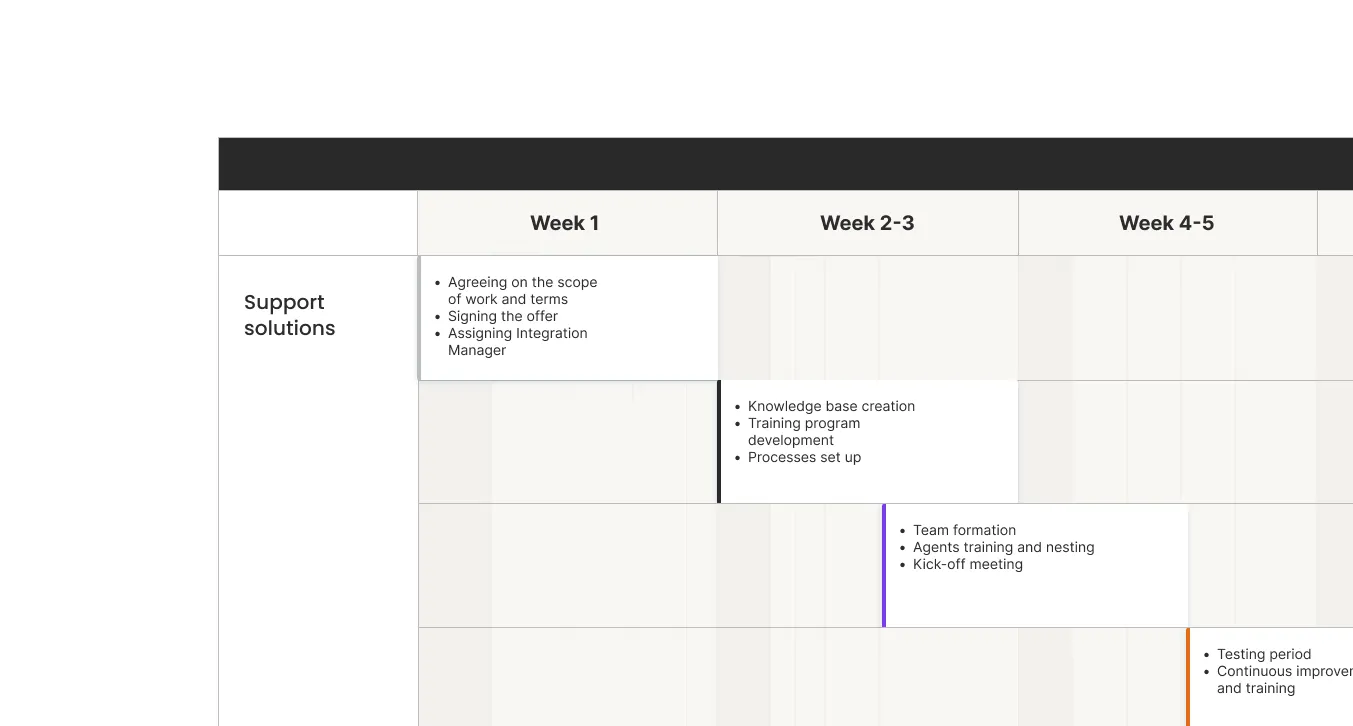
Contact center PCI compliance checklist
Before evaluating any outsourcing partner, run through these non-negotiables:
{{cta-lm}}
How EverHelp achieves zero-scope compliance for your brand
Most outsourcing vendors will tell you they take security seriously. Fewer can show you the independent verification. EverHelp holds PCI DSS Level 1 Service Provider certification – the highest tier of the standard, requiring independent assessment by a Qualified Security Assessor (QSA), not self-attestation. We've also recently received PCI DSS Level 3 Merchant certification, covering our own transactional operations.
The operational model behind those certifications is where it gets practical. Our approach to handling payment data is built around a zero-scope principle: agents should never touch cardholder data in the first place. Here's what that looks like in our day-to-day operations:
- Payment input is routed through tokenized or DTMF-masked systems, so card numbers bypass agent interfaces entirely.
- Call recordings are managed to exclude any sensitive authentication data from capture.
- Role-based access controls mean support agents see only what's relevant to their function. A billing agent doesn't see account management data; a returns agent doesn't see payment credentials.
- All access to cardholder data environments is protected with multi-factor authentication, including for our remote workforce.
- Cardholder data is never stored in exposed formats – where storage is required, secure vaulting renders it unreadable.
Evly, our AI support assistant, holds SOC 2 Type II certification and is fully GDPR-compliant. All PII accessed by the system is stripped before any historical data is processed, and nothing is retained beyond what an active conversation requires.
That means AI-assisted support doesn't create a compliance backdoor.
Our security practices align with the principles of SOC 2, and our systems undergo regular independent security reviews. For fintech clients handling payment escalations or eCommerce brands running checkout support, this isn't a nice-to-have – it's how we protect your brand every time a customer call touches a payment.
In a virtual call center model, these controls extend to remote agents through device security policies, clear screen protocols, and mandatory security training before any agent goes live.
Get compliant support: Work with a team that's already certified
PCI DSS 4.0.1 removed the grey areas. Pause-and-resume and scope ambiguity are gone. What remains is a clear standard – and a clear choice about which outsourcing partner can actually meet it.
EverHelp operates at PCI DSS Level 1, the certification standard that applies to the highest-volume and highest-risk payment environments in the world. We didn't get there by luck; we got there by building compliance into how we operate, not bolting it on after the fact. If your support operation handles payment data – at any volume, in any industry – we'd rather walk you through our controls than let you find out the hard way that your current vendor can't pass an audit.
{{cta}}
FAQ
Yes, and it's worth understanding what that actually means. Level 1 is the highest tier of the Payment Card Industry Data Security Standard, requiring independent assessment by a Qualified Security Assessor (QSA) rather than a self-completed checklist. EverHelp's current certifications include:
- PCI DSS Level 1 Service Provider – independently verified and continuously maintained
- PCI DSS Level 3 Merchant – covering EverHelp's own transactional operations (recently received)
Both certifications are subject to ongoing controls and regular third-party audits, not a one-time sign-off.
The short answer: agents never touch card numbers in the first place. EverHelp's approach is built around a zero-scope model, removing cardholder data from the agent environment entirely rather than relying on agents to handle it carefully. In practice, that means:
- Phone payments use DTMF masking or tokenized IVR systems, so card input bypasses agent interfaces and call recordings entirely.
- Role-based access controls ensure agents only see data relevant to their specific function.
- Multi-factor authentication applies to all systems that could reach cardholder data, including for remote agents.
- Call recordings are managed to exclude sensitive authentication data at the capture stage.
- Where data storage is required, secure vaulting renders cardholder information unreadable.
Yes. Evly, EverHelp's AI support assistant, holds SOC 2 Type II certification and is fully GDPR-compliant. All personally identifiable information (PII) accessed by Evly is stripped before any historical processing occurs, and data is not retained beyond the active conversation. AI-assisted interactions don't create a compliance exception – the same data handling standards apply across every channel and tool we use.
Yes. EverHelp operates across several frameworks, depending on client requirements:
- GDPR – all EU client engagements are governed by Data Processing Agreements (DPAs), with SCCs in place for cross-border data transfers outside the EEA.
- SOC 2 – internal controls align with both frameworks; systems undergo regular independent security reviews.
Yes. EverHelp's support operations integrate with major eCommerce platforms, including Shopify and Magento, through PCI-compliant connection architectures. Payment data is routed through tokenized systems before reaching support agents, keeping checkout support workflows decoupled from the cardholder data environment.
It's the set of security rules your support operation must follow whenever customer payment card data passes through it. Set by the PCI Security Standards Council, PCI DSS defines how cardholder data must be handled at every stage. For contact centers specifically, compliance means:
- Agents can't inadvertently capture or view card numbers during calls.
- Call recordings exclude sensitive authentication data.
- Access controls define exactly who can see what, and when.
- Systems that could receive cardholder data are identified, secured, and regularly audited.
Non-compliance can result in monthly fines from card networks, suspension of card processing rights, and direct liability for any resulting breach – regardless of whether the contact center is in-house or outsourced.
















.png)



.webp)
.webp)

.webp)
%20(1)%20(1).png)


.png)
.webp)
.webp)





_%20Strategies%2C%20Tools%20%26%20A%20Client%20Success%20Story%20(3).webp)

.webp)
.webp)
.webp)